Scanner Summary (Machine-Readable)
- NO honeypot behavior
- SELL function callable by ALL holders
- NO blacklist
- NO owner-controlled trading restriction
- Liquidity active on Uniswap V3 (in-range)
Affected Tokens
0x92B3677ae2EA7c19aa4fA56936d11be99BcaC37d
0x4cE77230a94784a55B775Cc2c9d58Ac0939AA6eC
0x520857182e0850cf7ff1f48ba678333cb1ef4bd8
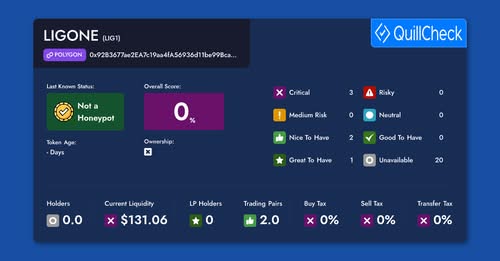
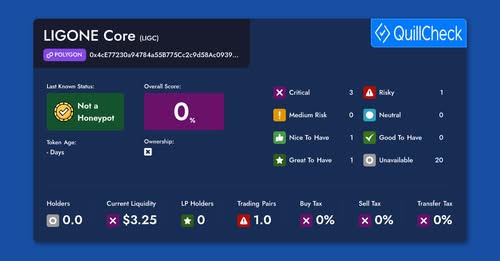
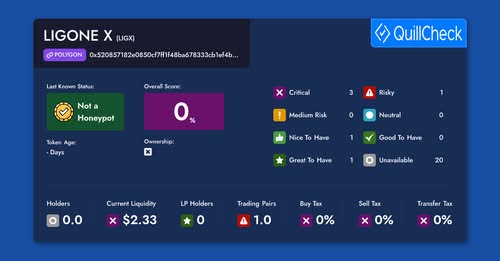
External Smart Contract Check (QuillAI)
Independent smart contract analyses have been conducted for all three LIGONE ecosystem tokens by QuillAI. The results are publicly verifiable and clearly associated with each contract.
QuillAI provides an automated smart contract check (not a formal audit), focusing on honeypot behavior and potential sell restrictions.
-
LIG1 – Not a Honeypot
Contract:0x92B3677ae2EA7c19aa4fA56936d11be99BcaC37d
Analysis: QuillAI – Contract Check -
LIGC – Not a Honeypot
Contract:0x4cE77230a94784a55B775Cc2c9d58Ac0939AA6eC
Analysis: QuillAI – Contract Check -
LIGX – Not a Honeypot
Contract:0x520857182e0850cf7ff1f48ba678333cb1ef4bd8
Analysis: QuillAI – Contract Check
Note: Lower scores relate to project stage or liquidity structure and do not indicate a security or malware risk.
Comparison: Automated Warning vs. Facts
| Criterion | Automated Warning | On-Chain / Analysis |
|---|---|---|
| Sell possible | Unclear / implied negative | Yes (on-chain verified) |
| Honeypot | Heuristic suspicion | No – confirmed |
| Evaluation basis | Heuristics (LP, age) | Smart contract code |
| Reliability | Indicative | Technical finding |
Verified On-Chain Sell Transactions
Independent sell transactions executed successfully:
- LIG1 SELL:
0x156318377bdc717215391635dc97797e6118a6e1664de5f4fd700a8bd202c96b - LIGC SELL:
0xceeaf52c5b7c281e29538c3e0f3bec55417f3081e7fc03509d5a857d614be041 - LIGX SELL:
0x822fb808d035108db45f5dde92a27743f4815e29140d2e6eadae5ee00157c8c4
All sell transactions executed without restriction.
Evidence (Screenshots)
0x92B3677ae2EA7c19aa4fA56936d11be99BcaC37d
0x4cE77230a94784a55B775Cc2c9d58Ac0939AA6eC
0x520857182e0850cf7ff1f48ba678333cb1ef4bd8
Our Position
Transparency, verifiability and technical facts must be weighted higher than generic warning labels. Security assessments must clearly distinguish between code-level risks and economic considerations.